What is a Virtual Chief Information Security Officer (vCISO)?
A Virtual Chief Information Security Officer (vCISO) is an outsourced security expert or service provider who fulfills the role of a Chief Information Security Officer (CISO) without being a full-time, in-house employee.
A vCISO provides strategic leadership, guidance, and oversight for an organization's information security program, including policy development, risk management, compliance support, incident response planning, and vendor risk assessment.
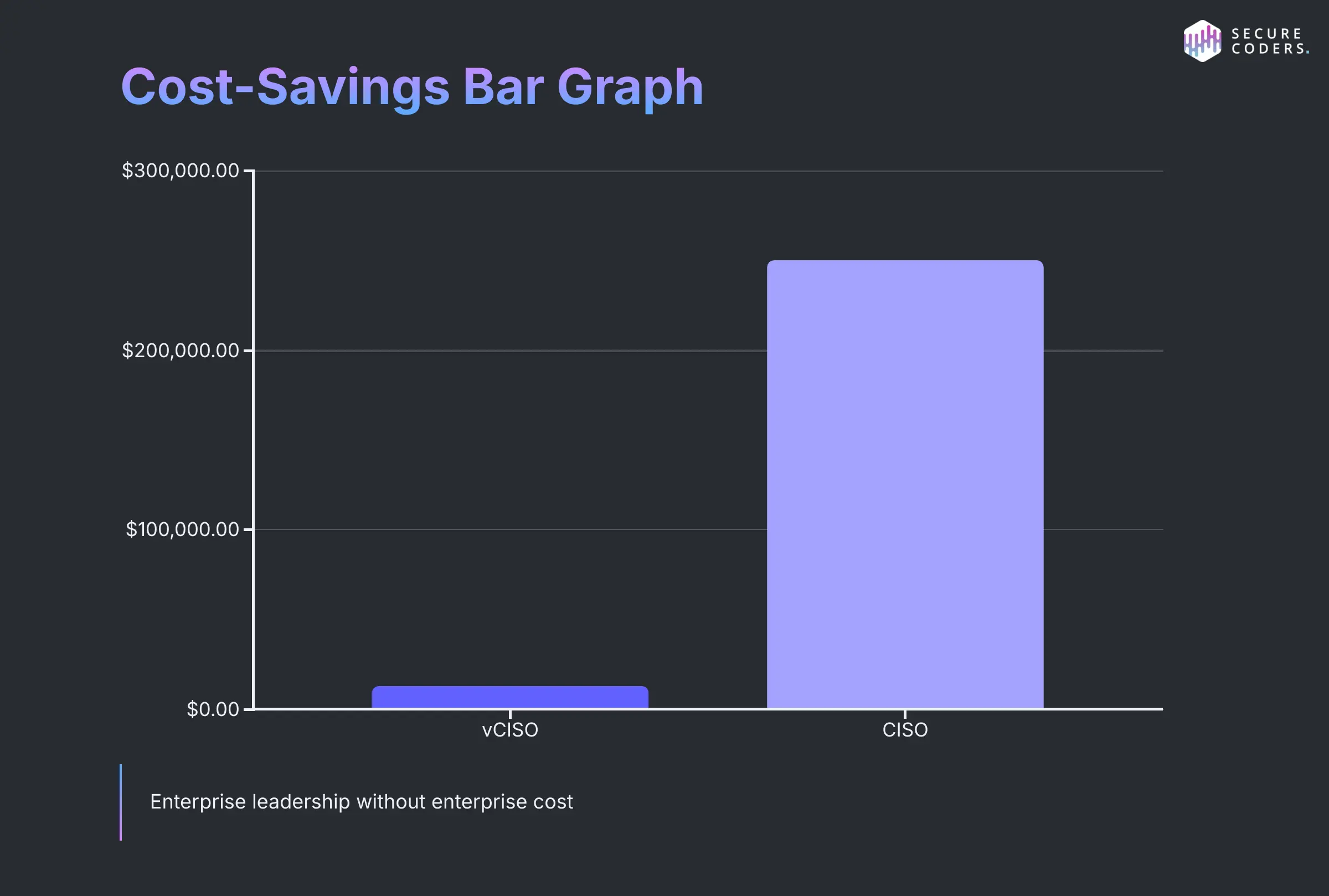
For many small to mid-sized businesses, hiring a full-time CISO can be prohibitively expensive, with salaries often exceeding six figures.
A vCISO offers a cost-effective alternative, delivering the same level of expertise and leadership on a part-time, contract, or as-needed basis.
This flexibility allows organizations to access high-level security capabilities without the financial burden of a permanent executive hire.
In addition to cost savings, vCISOs bring the advantage of broad industry experience, having worked across multiple organizations and sectors.
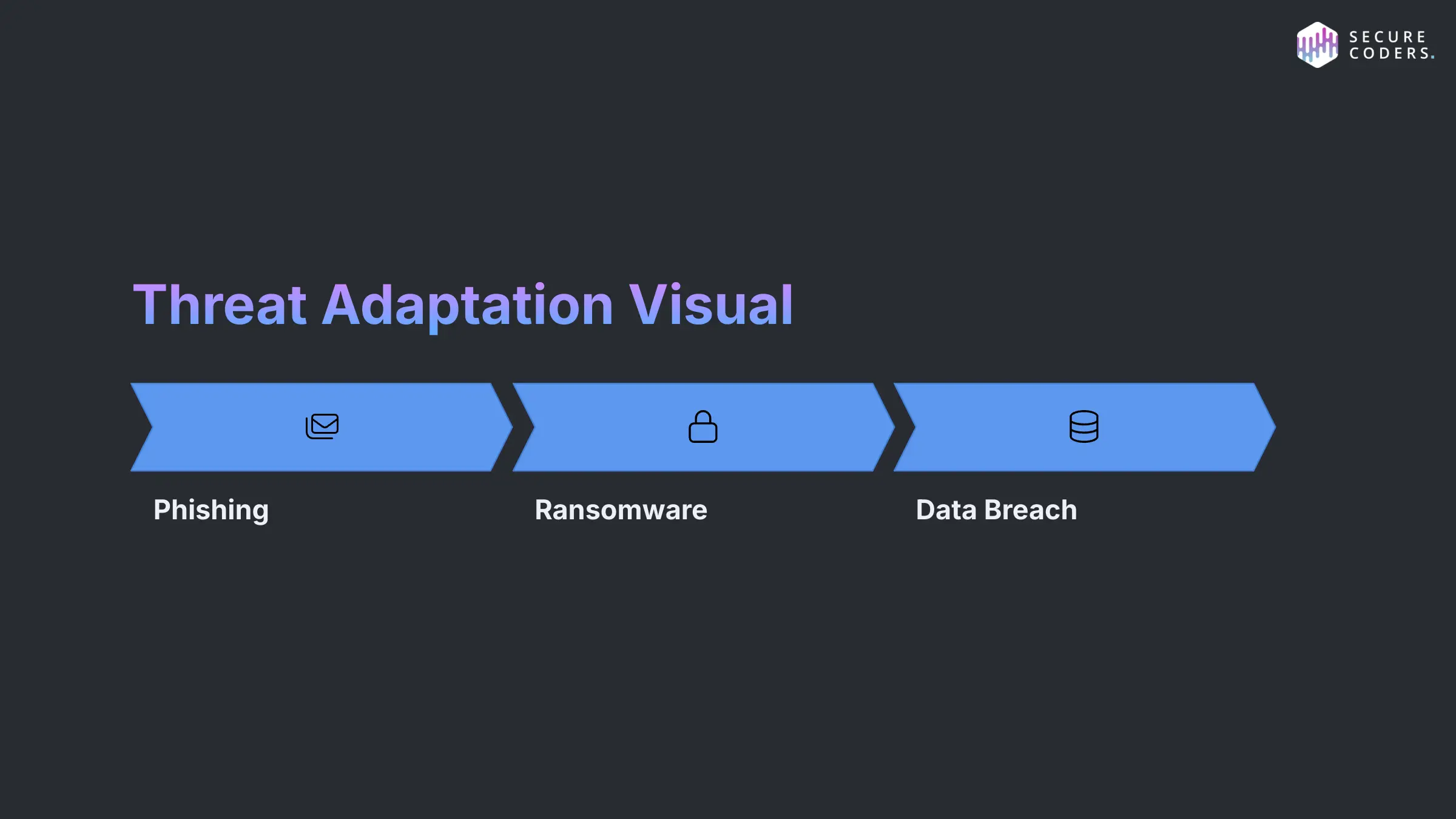
They stay up to date with evolving threats and compliance requirements and can tailor security strategies to meet specific business needs.
Whether leading compliance initiatives like SOC 2 or HIPAA, responding to incidents, or preparing for audits, a vCISO provides the expertise needed to build and maintain a robust cybersecurity posture—making them an ideal solution for businesses seeking security leadership without the full-time commitment.
What are vCISO Roles & Responsibilities?

A vCISO plays a critical role in helping organizations develop, implement, and manage a comprehensive cybersecurity program.
As an outsourced security executive, the vCISO provides leadership and strategic direction across key areas such as security strategy, compliance, risk management, and incident response—without the cost of a full-time, in-house hire.
According to Gartner the role of vCISO or CISO is to enable digital business by driving the critical initiatives that secure and protect the enterprise.
One of the vCISO's primary responsibilities is to define and oversee the organization's security strategy.
This includes evaluating the current security posture, identifying gaps, and developing a roadmap to align cybersecurity efforts with business goals.
The vCISO ensures that security initiatives are prioritized based on risk and integrated across the organization's operations.
In the area of compliance, the vCISO helps organizations meet regulatory and industry-specific requirements such as GDPR, HIPAA, PCI DSS, or SOC 2.
They provide guidance on preparing for audits, maintaining documentation, and implementing policies and controls to demonstrate compliance.
Risk management is another core responsibility for vCISO's.
A vCISO conducts risk assessments to identify and analyze potential threats, evaluates the effectiveness of existing controls, and recommends mitigation strategies.
This includes third-party vendor risk management and ensuring that the organization's supply chain meets security standards.
When it comes to incident response, a vCISO develops and maintains response plans to quickly detect, contain, and recover from security incidents.
They coordinate with internal teams and external partners during breaches, conduct post-incident reviews, and use findings to improve preparedness.
Additionally, a vCISO often leads security awareness training, advises on security tools and technologies, and acts as a liaison between technical teams and executive leadership.
Overall, a vCISO provides expert-level cybersecurity leadership tailored to the organization's size, risk profile, and budget—enabling companies to strengthen their defenses without the cost and complexity of hiring a full-time CISO.
When to hire a vCISO?
Hiring a vCISO is a strategic decision that can benefit organizations at various stages of growth and in different circumstances.
Knowing when to bring in a vCISO is key to strengthening security posture, maintaining compliance, and building trust with stakeholders.
One common scenario is organizational growth. As a company expands—especially into new markets or regions, it faces increased cybersecurity risks and regulatory requirements.
A vCISO helps scale security strategies to match growth, ensuring that new systems, processes, and vendors are properly secured.
Upcoming audits or compliance initiatives are another reason to engage a vCISO.
Whether preparing for SOC 2, HIPAA, GDPR, or ISO 27001, a vCISO can lead the development of policies, conduct gap assessments, and oversee audit readiness, ensuring the organization meets its compliance obligations without diverting internal resources.
If an organization has no internal CISO, hiring a vCISO provides immediate access to seasoned security leadership.
Small to mid-sized businesses often lack the budget for a full-time CISO, making a virtual one an affordable and flexible alternative that brings expert insight without long-term overhead.
Security incidents or breaches are also triggers for engaging a vCISO. In the aftermath of an incident, a vCISO can assess what went wrong, lead response efforts, and build a stronger, more resilient security framework to prevent future events.
Finally, as organizations work to build trust with customers, partners, or investors, a vCISO adds credibility.
Demonstrating that a dedicated security expert is overseeing cybersecurity efforts reassures stakeholders that the company takes data protection seriously.
In all these scenarios, a vCISO delivers expert guidance and scalable solutions, helping organizations protect their data, reputation, and long-term business success.
What are the benefits of hiring a vCISO over having no Chief Information Security Officer?
Hiring a vCISO offers significant advantages over operating without any dedicated security leadership.
For organizations that lack the resources for a full-time Chief Information Security Officer, a vCISO provides a cost-effective, strategic alternative that delivers expert guidance and measurable value.
One of the biggest benefits is return on investment (ROI).
A vCISO brings executive-level cybersecurity expertise at a fraction of the cost of a full-time CISO.
This allows organizations to access high-level strategic planning, risk management, compliance oversight, and incident response leadership without the financial burden of a permanent hire.
Over time, a vCISO helps prevent costly security incidents, improve compliance outcomes, and reduce operational risks—yielding a high ROI through avoided losses and regulatory penalties.
Flexibility is another key advantage. A vCISO can be engaged part-time, on-demand, or project-based, scaling with the company's needs.
Whether it's leading a compliance initiative, responding to an incident, or helping build a long-term security roadmap, the vCISO adapts to your business goals and budget.
A vCISO also provides an unbiased, external perspective. Unlike internal staff who may be influenced by organizational politics or blind spots, a vCISO evaluates security objectively and delivers candid, expert recommendations.
This helps organizations identify hidden vulnerabilities, optimize controls, and align cybersecurity efforts with business priorities.
In contrast, organizations without any form of CISO leadership often lack direction in managing cybersecurity risks, leading to inconsistent policies, regulatory exposure, and a reactive rather than proactive approach.
Without expert guidance, even well-intentioned IT teams may miss critical gaps in security.
In short, hiring a vCISO empowers organizations with expert-level security leadership, strategic clarity, and scalable support—ensuring a strong cybersecurity foundation without the long-term commitment of a full-time executive.
What are some challenges and/or limitations of hiring a vCISO?
While hiring a vCISO offers flexibility and cost savings, there can be challenges and limitations to consider.
One concern may be that a vCISO is not always full-time. This can limit their ability to immerse themselves in the company's culture or respond immediately to time-sensitive security issues.
Without being physically embedded in day-to-day operations, a vCISO may miss subtle organizational dynamics or real-time developments that could affect security decisions.
Remote working barriers such as a lack of onsite presence can also pose challenges. Communication delays, time zone differences, or reliance on virtual meetings may hinder collaboration with internal teams or slow the resolution of issues.
Security decisions often require coordination across departments, and virtual interactions may lack the immediacy of face-to-face engagement.
Another limitation is the vCISO's capacity**.** Because most serve multiple clients, their availability may be constrained during critical periods, such as during a breach or audit preparation. Organizations may need to supplement vCISO services with internal resources for full coverage.
Finally, some stakeholders may prefer a dedicated, in-house CISO for perceived stability, stronger alignment with long-term strategy, and deeper organizational involvement.
Despite these limitations, many businesses find the trade-offs acceptable for the expertise and affordability a vCISO provides.
What is the difference between a vCISO and a CISO?
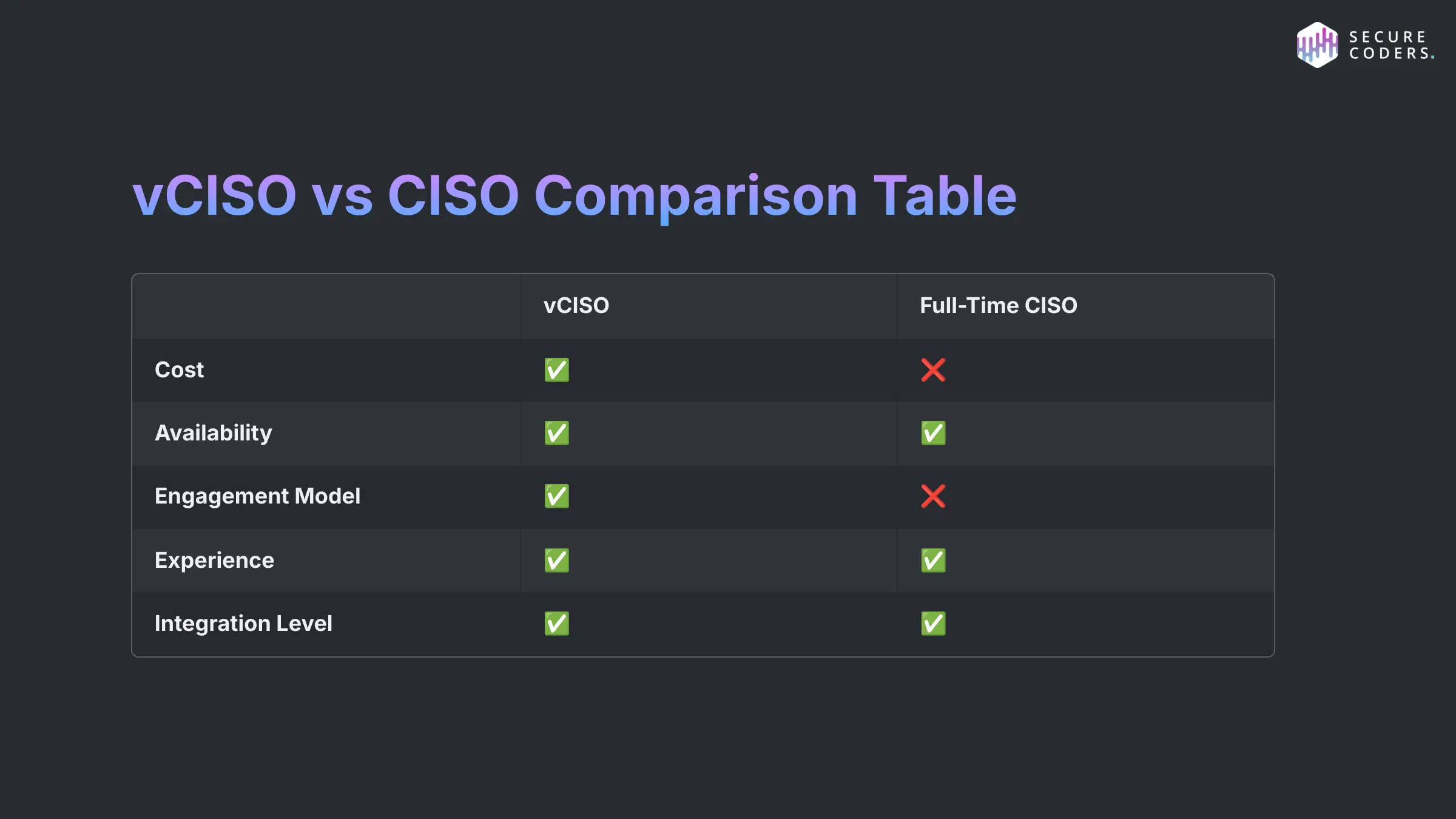
A Virtual Chief Information Security Officer (vCISO) is an outsourced security leader who provides strategic cybersecurity guidance on a part-time or contract basis, offering flexibility and cost savings for organizations that don't need or can't afford a full-time executive.
In contrast, a Chief Information Security Officer (CISO) is a full-time, in-house executive responsible for developing and managing the organization's cybersecurity strategy, policies, and incident response.
While both roles focus on protecting information assets and ensuring compliance, a vCISO typically serves multiple clients and may have limited availability, whereas a CISO is fully dedicated to one organization's security needs.
What are the different engagement models for vCISO's?
Organizations looking to hire a vCISO can choose from various engagement models based on their specific needs, budget, and level of required involvement. The most common models include hourly rate, retainer-based, and project-based engagements.
1. Hourly Rate Model
This model allows organizations to pay the vCISO only for the time worked. It's ideal for short-term needs such as reviewing a security policy, answering a security questionnaire, or advising on compliance. The hourly rate model offers flexibility and control over costs but may not be suitable for long-term strategic initiatives, as it doesn't guarantee availability or continuity.
2. Retainer Model
In a retainer-based engagement, the organization pays a fixed monthly fee for a set number of hours or ongoing advisory access. This model is beneficial for companies needing continuous support, such as regular risk assessments, incident response planning, or executive reporting. It provides predictable costs and ensures consistent involvement from the vCISO, making it suitable for growing businesses or those with evolving security needs.
3. Project-Based Model
This engagement is structured around a specific scope of work—such as achieving SOC 2 compliance, developing an information security program, or leading a post-breach remediation effort.
The vCISO is contracted for the duration of the project with clearly defined goals, deliverables, and timelines. This model is ideal for organizations seeking focused expertise to complete a major security initiative without committing to an ongoing relationship.
Each model offers distinct advantages depending on the organization's size, maturity, and objectives. Selecting the right engagement model ensures cost-efficiency while gaining expert guidance to strengthen the company's cybersecurity posture.
How has SecureCoders helped organizations with vCISO services?
Securecoders has provided vCISO services for many of its customers across industry verticals and in highly regulated industries.
One specific customer was a Global Clinical Trial Supply & Pharmaceutical Commercial Services organization in Pennsylvania, which had an information security program which lacked maturity in the areas of operational security, governance, risk and compliance.
Their goal was to find a vendor that would rebuild their program from the ground up by working with the Director of IT to implement new processes and specific technology that better secured their organization and aligned with their business objectives.
How SecureCoders Helped
To help manage their goals and better understand the unique needs of the organization SecureCoders proposed and executed a Virtual Chief Information Security Officer (VCISO) security program development residency to ensure the right steps were taken to implement the new information security program.
Key Solutions Delivered
SecureCoders was able to determine the gaps in the existing information security program and accomplished the following:
Provide cybersecurity and risk leadership support to the Director of IT
Give Direction in creating and updating a multi-year cybersecurity roadmap
Review and change the existing security infrastructure to aide in risk reduction
Work with quality assurance and external customers to facilitate audit processes and build customer trust
Develop program strategies, solutions and product recommendations for:
Security awareness training and phishing
Managed Detection and Response
Vulnerability Management
Security program alignment with ISO27001
Email and Network Security
Annual Penetration Testing
Manage security vendor relationships and purchases of new information security tools and services
Build Incident response function and respond to escalated security alerts
Results and Business Impact
Through our VCISO residency, we were able to deliver on the various needs of the organization and the Director of IT. Securecoders successfully improved operational security, governance, risk and compliance program, leaving the organization with the following in place:
- Quarterly Risk and Governance Committeement presentations
Implementation of various programs and tools, including:
- A Vulnerability Management and remediation program
- Global implementation of Multi-factor Authentication tools and processes
- A multi-year security awareness program
- An IT Security and Privacy vendor process and questionnaire
- Transitioned endpoint security solutions, to reduce the risk of malware exploits in the wild
- Implementation of a new email security product
- Annual penetration tests and associated reports
Reduction and remediation of audit findings
A vetted list of technology vendors, that advised on risk and security implementation practices
Maintained information security monitoring tools, which include the implementation of a managed security services provider
Completed security program integration of two acquisitions
Are you interested in hiring a Virtual Chief Information Security Officer (VCISO)?
Strengthen your cybersecurity posture with expert leadership—hire a Virtual Chief Information Security Officer through SecureCoders today. Gain strategic security guidance, ensure compliance, and protect your data without the cost of a full-time executive.
Get started now and secure your business with confidence.

